A critical Linux kernel vulnerability was publicly disclosed on April 29, 2026. We want to be straight with you about what it is, what we have already done on your behalf, and what action you need to take right now.
What is this about?
Copy Fail (CVE-2026-31431) is a Linux kernel bug that has been sitting there since 2017. Any user with shell access to your server can use it to get full root. No special skills, no race conditions, no compiled tools. Just a tiny Python script. It works on every major Linux distribution including Ubuntu 24.04, 22.04 and 20.04.
Who should pay attention?
If your server has multiple SSH users, runs web apps with any shell access, or has Docker containers on it, this is high priority for you. Single-user servers are at lower risk but should still be patched.
What we already did
Mitigation pushed to your servers
We pushed an interim fix to all servers we could reach through the RunCloud agent. It blocks the vulnerable kernel module from loading and closes the attack surface without requiring a reboot.
Some servers could not be reached at the time. This happens when a server was offline, had the agent stopped, or had firewall rules blocking agent communication. If your server was in that group, you need to apply the fix manually.
Check if your server is protected
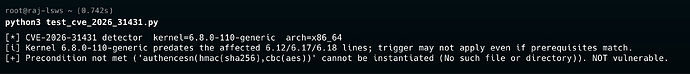
Run the detection script yourself to be sure
curl -O https://raw.githubusercontent.com/rootsecdev/cve_2026_31431/main/test_cve_2026_31431.py
python3 test_cve_2026_31431.py
You want to see: NOT vulnerable
If your server is still vulnerable, fix it now
echo “install algif_aead /bin/false” | sudo tee /etc/modprobe.d/disable-algif.conf
sudo rmmod algif_aead 2>/dev/null || true
Then confirm it worked:
python3 test_cve_2026_31431.py
Will this break anything?
No. We tested this thoroughly. Nginx, PHP, MySQL, SSH and SSL all continue working normally. The fix also survives reboots so you do not need to reapply it.
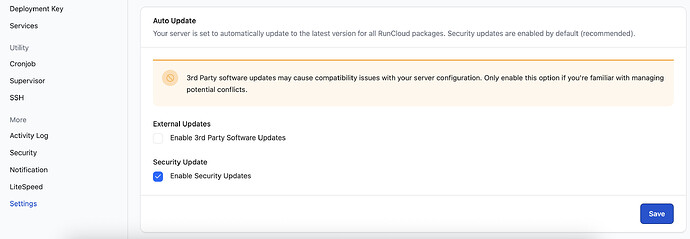
Keep Security Updates Turned On
Go to your Server’s Settings → Auto Update and make sure Enable Security Updates is checked. This is enabled by default but worth double checking. This is what allows critical kernel and security patches to be applied to your server automatically. If it is off, your server will not receive updates.
The permanent fix
Waiting on Ubuntu…
Ubuntu has not released the official patched kernel yet as of today. We are watching their tracker. The moment it is out, we will notify you and it will show up as a kernel update in your dashboard.
Keep an eye on this page for Ubuntu’s official patch:
ubuntu.com/security/CVE-2026-31431
When it is available, update and reboot:
sudo apt update && sudo apt upgrade -y
sudo reboot
After the reboot, remove the interim fix. If your server was patched by us, we will handle this automatically once the official Ubuntu kernel update is applied. If you applied the fix manually, run these to clean up:
sudo rm /etc/modprobe.d/disable-algif.conf
sudo modprobe algif_aead
python3 test_cve_2026_31431.py
Once you are on the patched kernel and everything is confirmed clean, remove the detection script you downloaded earlier. It is not harmful to leave it but there is no reason to keep it around once you are done.
rm ~/test_cve_2026_31431.py
References
- Technical writeup by the team that found it: xint.io/blog/copy-fail-linux-distributions
- Official repo: github.com/theori-io/copy-fail-CVE-2026-31431
- Ubuntu CVE tracker: ubuntu.com/security/CVE-2026-31431
If you have questions, reply below or contact our support team directly. We will keep this post updated as things develop.